Understanding the Infector Virus and Protecting Your Digital Life
In the vast landscape of cybersecurity threats, few are as persistent or as damaging as the infector virus. Unlike the flashy ransomware attacks that make headlines or the stealthy spyware that lurks in the background, the infector virus operates with a specific, sinister purpose: to spread. It is the digital equivalent of a contagious disease, attaching itself to clean, healthy files and turning them into carriers of chaos. For the average computer user, understanding this threat is the first step in building a robust defense against data loss and identity theft.
To truly grasp the danger, we must look at both the biological world that inspired the name and the technical reality of these malicious programs. Just as a biological virus hijacks a living cell to reproduce, an infector virus hijacks a computer’s legitimate files . However, unlike a biological virus that might simply cause a sneeze, a file infector can dismantle your operating system, steal your private documents, and convert your machine into a zombie under the control of remote hackers.
What Exactly is an Infector Virus?
In the realm of cybersecurity, the term "infector" is often shorthand for a "file infector virus." This category of malware is defined by two specific criteria: execution and replication . To be classified as a true virus, the code must execute itself (usually by tricking the user into running a legitimate program) and it must replicate itself to spread to other files.
These viruses are meticulously designed to target executable files. On a Windows computer, this primarily means files with extensions like .exe (applications) or .scr (screensavers) . When a user downloads an infected program from an untrustworthy website or plugs in a USB drive containing a compromised setup file, the clock starts ticking. The moment the user launches that program, the virus activates.
The infector virus employs various methods to attach itself to a host. Some "prepend" themselves to the beginning of a file, while others "append" their code to the end. More sophisticated variants use "cavity" techniques, inserting themselves into empty spaces within the file’s code to avoid changing the file’s size—a clever trick to bypass basic security scans .
The Many Faces of an Infector
Not all infector viruses are created equal. Over the decades, these threats have evolved into distinct types, each with a unique method of attack. Understanding these categories helps illustrate why a multi-layered security approach is necessary.
1. File Infectors (The Classic Attack)
This is the most common type. These viruses target application files. A notorious example from the past is the Jerusalem virus, but modern variants are far more dangerous. Once a file infector runs, it searches the hard drive and network shares for other .exe files to corrupt. If you share an infected document or program via email or cloud storage, you are unknowingly spreading the plague to your colleagues and family .
2. Boot Sector and Master Boot Record (MBR) Viruses
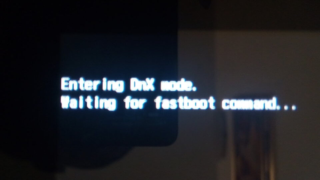
These are the heavy hitters of the virus world. Instead of targeting files, they attack the critical startup sector of a hard drive. The boot sector contains the code that tells your computer how to start the operating system. An infector virus targeting this area loads into memory the instant you turn on the PC, even before the operating system loads. This allows the virus to hide deeply within the system, making it incredibly difficult to remove. Even reformatting the main drive might not kill an MBR infector, as it resides in the master boot record .
3. Multipartite Viruses
Why choose one target when you can have both? Multipartite viruses are a hybrid threat. They simultaneously infect boot sectors and executable files. This duality makes them particularly resilient. If you clean the executable files but leave the boot sector infected, the virus will immediately reinfect your clean files the next time you restart the computer .
4. Polymorphic Viruses (The Shapeshifters)
This is where the threat becomes truly sophisticated. Polymorphic viruses, such as the infamous Sality or Virut, have the ability to change their code signatures every time they replicate . Traditional antivirus software works by matching code to a database of known "signatures." A polymorphic infector virus mutates its code, making it invisible to signature-based detection. It encrypts its body and changes the decryption key with each infection, allowing it to evade security software for extended periods.
The Damage: More Than Just a Slow Computer
Many users assume a virus is merely a nuisance that slows down their PC. While system lag is a symptom, the reality of an infector virus infection is often far more sinister. Modern infectors are rarely built for pranks; they are built for profit.
Data Theft and Espionage
When a virus like Ramnit infects a system, it doesn't just replicate. It searches for sensitive information. This includes saved FTP credentials (passwords for website servers), email logins, and browser cookies. Hackers use these stolen credentials to break into bank accounts, social media profiles, and corporate networks .
The Backdoor Threat
Many file infectors download additional payloads known as "backdoors" or "RATs" (Remote Access Trojans). Once the infector virus establishes a foothold, it reaches out to a command-and-control server (C&C) to download other types of malware. Your computer might suddenly become part of a botnet, sending spam emails or attacking other websites without your knowledge. In some cases, the virus deletes files or corrupts the hard drive partition, leading to total data loss.
How to Detect an Infection
How can you tell if your system is harboring an infector virus? Unlike the movies, there is usually no "HACKED" sign that flashes on the screen. Instead, look for these subtle signs:
-
Unexplained File Changes: You notice that file names have changed, or icons for your programs have been replaced with generic icons.
-
Application Errors: You try to open Word or your web browser, and it crashes immediately or fails to launch, because the executable has been corrupted.
-
High CPU Usage: You open the Task Manager and see 100% disk or CPU usage, even though you have no programs open. The virus is busy replicating itself in the background.
-
Missing Storage Space: The virus is adding its code to thousands of files, slowly eating up your hard drive space.
Fortifying Your Defenses
Protecting yourself from an infector virus does not require a degree in computer science, but it does require discipline. Since these viruses rely on tricking the user into executing a file, your behavior is your strongest firewall.
1. Treat Unknown Files Like Strangers
Do not open email attachments from senders you do not recognize. Be especially wary of executable files sent via messaging apps or downloaded from pop-up ads. If you receive a strange link from a friend, confirm with them via phone or text before clicking—their account may be infected and sending the virus to everyone on their contact list.
2. Disable Macros and Scripts
Many infector viruses spread through Microsoft Office documents using malicious macros. Unless you work in a corporate environment that specifically requires them, keep macros disabled by default .
3. Keep Everything Updated
Cybercriminals exploit known holes in software. If you delay updating your Windows operating system or your web browser, you are leaving the door open for an infector virus. Enable automatic updates to ensure you receive security patches as soon as they are released .
4. Use a Layered Security Approach
You need an antivirus program that offers real-time protection and behavioral analysis. While free antivirus options offer basic protection, investing in a robust security suite that includes heuristic analysis (which looks for suspicious behavior rather than just signatures) is crucial to catch polymorphic viruses . Additionally, enable the built-in firewall in your operating system to block unauthorized outbound connections—this can stop an infector from "phoning home" to hackers if it manages to breach your system.
The Evolution of the Threat
The infector virus is a relic of early computing that has been refined into a modern weapon. In the late 90s and early 2000s, viruses like CIH (Chernobyl) were designed to destroy data. Today, families like Sality and Virut are designed to persist and control. According to security reports, even as ransomware dominates the news, file infectors remain a top threat, accounting for a significant percentage of global malware infections .
These viruses have adapted to 64-bit systems and cloud environments. They can now search network drives and USB sticks automatically, ensuring that even air-gapped computers (computers not connected to the internet) can be compromised by an infected USB drive. The persistence of the infector virus serves as a reminder that digital hygiene is not a one-time setup but a continuous practice.
Conclusion
In the digital age, knowledge is the ultimate antivirus. The infector virus remains one of the most dangerous classes of malware because it exploits the most common human action: opening a file. By understanding how these viruses spread—through executable files, boot sectors, and macros—you can take proactive steps to protect your digital sanctuary.
Stay vigilant, back up your critical data to an external drive that is not always connected to your computer, and ensure your security software is always active. The fight against digital infection is ongoing, but with the right habits, you can ensure your files remain yours alone.
-
Digital Security Trends: Cybersecurity Threats You Need to Know in 2025
-
Protecting Assets: How to Secure Your Online Data
-
Tech Guides: Understanding Modern Malware Protection
For a deeper technical dive into the history of computer viruses and the evolution of file infectors, you can explore the detailed archives on Wikipedia's Timeline of computer viruses.