Imagine a digital room with ten million doors. Every second, thousands of people open a random door. You have absolutely zero idea who is standing on the other side.
That is the fundamental engineering nightmare of random video chat.
Connecting two strangers across the globe in milliseconds is technically easy. Keeping those two strangers safe from each other is a monumental, exhausting logistical puzzle. The internet is full of bad actors looking for an easy target.
For years, the industry standard was simply to look the other way. Platforms built the room, unlocked the doors, and let the users fend for themselves.
That era is over. Today, we are pulling back the curtain. Here is an honest, technical look at exactly how modern platforms keep your camera feed secure, and why your digital privacy is the only thing keeping this entire industry alive.
The Omegle Collapse: A Lesson in Negligence
You cannot discuss online privacy without analyzing the biggest failure in the history of the niche.
For over a decade, CooMeet was the undisputed giant of random chat. It was a cultural phenomenon. It was also a massive, unmoderated security hazard.
The platform operated on a philosophy of absolute anarchy. There were no accounts, no real moderation algorithms, and no consequences for malicious behavior. You clicked a button, and you took your chances.
Eventually, that negligence caught up with them. The internet changed. Users demanded safer environments, and regulatory bodies started paying attention. When Omegle finally shut down, it wasn’t just the end of a website. It was the end of the unmoderated internet.
It proved a hard truth: if a platform does not actively protect its users, it will inevitably destroy itself.
How OmeTV Changed the Security Blueprint
When the giant fell, the landscape fractured. Millions of users were left looking for a platform that offered the thrill of random connection without the guaranteed exposure to cyber threats.
This is exactly where OmeTV stepped in and rewrote the blueprint.
Instead of treating moderation as an afterthought, OmeTV built its entire infrastructure around user accountability. They realized that you can still have spontaneous, anonymous fun while enforcing basic digital boundaries.
But how do you enforce rules on a platform built for anonymity? You don’t ask for ID. You use code.
The AI Bouncer at the Door
The first line of defense is not a human. It is a highly trained algorithm.
When you boot up OmeTV, the system instantly scans your camera feed. It is not recording your identity or saving your face to a database. It is looking for biological geometry.
The AI needs to verify two things: Are you a real human being, and is your face clearly visible in the frame?
If you try to point your camera at a blank wall, a pre-recorded video, or a static image, the system flags you instantly. The connection drops. The AI acts as a digital bouncer, keeping the automated bots and the scammers standing out in the cold.
Human Moderation vs. Machine Learning
Algorithms are incredibly fast, but they lack human context. An AI might flag a user for holding a weird prop, mistaking it for a terms-of-service violation.
This is why machine learning must be backed by a massive team of human moderators.
When a user clicks the “report” button, the system captures a temporary, encrypted snapshot of the interaction. A human moderator reviews the context. If a user is caught violating safety guidelines, their device is banned.
It is a constant, high-speed game of whack-a-mole, combining the speed of AI with the nuance of human judgment.
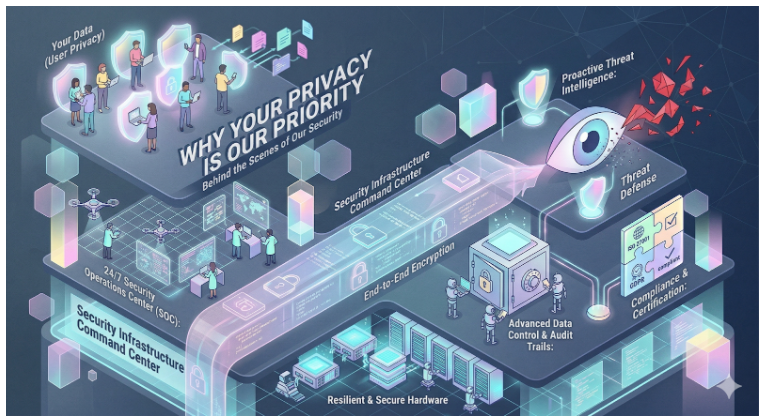
What Happens to Your Data? (The Uncomfortable Truth)
Privacy is not just about keeping you safe from other users. It is about keeping your data safe from the platform itself.
Users constantly ask: Is my video being recorded? Where does my IP address go? Who can see my location?
To answer this, you have to understand exactly how video routing works.
Peer-to-Peer vs. Server Relays
In the early days of the internet, random chats used Peer-to-Peer (P2P) connections. Your computer connected directly to the stranger’s computer.
This was incredibly fast, but it was a massive security flaw. Because you were directly connected, the other person could easily see your public IP address using basic network monitoring tools.
Modern, secure platforms rely on Server Relays.
When you use a platform like OmeTV, your video feed goes to a secure, encrypted server first. The server then relays that video to the stranger.
Your computer never actually touches their computer. The stranger only sees the IP address of the relay server, completely masking your actual location. Your data acts like a package passing through a secure sorting facility.
The Ephemeral Nature of the Feed
We do not want your video data. Storing millions of hours of high-definition video requires massive, expensive server farms.
From a purely financial standpoint, holding onto your data is a terrible business model.
Your video feed is ephemeral. It exists in the exact moment the connection is live. The second you click the skip button, that data packet is overwritten and destroyed. The only exception is when a direct report is filed, triggering a temporary, encrypted review.
Your privacy is protected by the sheer, overwhelming volume of the platform.
The “What-If” Scenarios: When the System Fails
No security architecture is flawless. Bad actors spend all day trying to reverse-engineer our defenses. You need to know exactly what happens when a threat slips through the cracks.
Here are the worst-case scenarios and the technical reality behind them.
What if someone uses a deepfake?
This is the fastest-growing threat in the digital space. Scammers use AI software to map a fake face onto their own movements, tricking the facial recognition algorithm into thinking they are a real user.
Our systems are constantly learning to detect the micro-tears and pixel distortions that deepfakes create. But if one fools the system, your best defense is your own eyes. Look for blurring around the jawline or glitches when they pass a hand in front of their face. Hit skip immediately.
What if a user bypasses the facial scan with a printed photo?
This used to work five years ago. It does not work today.
Modern algorithms require liveness detection. They look for micro-movements, eye blinks, and subtle shifts in lighting that a static piece of paper cannot replicate. If someone tries this, the camera feed simply refuses to connect them to the network.
What if you get IP-grabbed through a chat link?
While the video feed is routed securely, the chat box is still a vulnerability if you click external links.
If a stranger sends you a link to a “funny YouTube video,” and you click it, you are leaving the platform’s secure environment. That link could be an IP grabber, logging your location the second your browser opens the page.
The defense is simple: absolutely never click a link provided by a stranger in a random chat box. Ever.
Your Personal Security Tech Stack
The platform provides the walls and the security cameras. But you still need to lock your own front door.
You should never rely entirely on a corporation to handle 100% of your digital safety. You need a personal tech stack.
The Mandatory VPN
A Virtual Private Network is non-negotiable. Even with server relays protecting your direct connection, your internet service provider still knows what websites you are visiting.
A VPN encrypts your entire outbound connection. If a malicious actor somehow manages to scrape data, all they will find is a dummy server located in a different timezone. It is a five-dollar-a-month insurance policy for your digital life.
The Burner Identity
Never use your primary email address to sign up for chat platforms.
Create a dedicated “burner” email. Use a slight variation of your real name, or a completely fake one. If you decide to move a conversation over to Instagram or Discord, use a burner account there as well. Compartmentalize your digital footprint.
The Psychology of Moderation
There is a common misconception that strict security ruins the fun. People argue that moderation kills spontaneity.
The exact opposite is true.
When a platform is completely unmoderated, the environment becomes highly toxic. Normal, well-adjusted users log off because they are tired of being harassed. The only people left are the trolls and the bots. The platform dies.
Active moderation creates a digital safe haven. When you know you are not going to be exposed to illegal or highly disturbing content the second you click ‘Start’, your anxiety drops.
You actually engage more. You have better conversations. You laugh harder. Security is the foundation that allows genuine human connection to thrive.
Safety First: The Golden Rules of Anonymous Chat
We build the architecture, but you steer the ship. Here is how you navigate the waters safely.
Assume the camera is always recording. Even if the platform deletes your data instantly, the stranger on the other end might be running basic screen-recording software. Never do anything on camera that would ruin your professional or personal life if it ended up on the public internet tomorrow.
Guard your background architecture.
Do not broadcast from a room with highly identifiable features. Take down the framed diploma with your full name on it. Close the window blinds so people cannot cross-reference the skyline or the street signs outside your house.
Trust the power of the disconnect.
You owe absolute strangers nothing. If a conversation makes you feel slightly uncomfortable, do not try to be polite. Do not wait for a pause in the conversation. Use the skip button ruthlessly. It is your ultimate security tool.
The Future of Digital Privacy
The arms race between security architects and cyber-criminals will never end. As AI gets smarter, so will the bots. As encryption gets stronger, so will the attempts to crack it.
But the philosophy remains the same. Your privacy is not a luxury feature we offer to premium subscribers. It is the absolute core requirement for the platform to exist.
Without your trust, the entire ecosystem collapses.
We will keep upgrading the locks, training the algorithms, and banning the bad actors. All you have to do is log on, be smart, and enjoy the absolute unpredictability of the human race.